XPath1 Variable Extractor¶
XPath1 Variable Extractors lets you extract variables from HTML/XML responses using XPath1 queries.
Warning
XPath1 should be avoided for HTML extractions, CSS Selector Extractor is the correct and performing solution. Also, since JMeter 5.0 (september 2018) you should use XPath2 Extractor as it provides better and easier namespace management, better performances and support for XPath 2.0.
Extracting variables from HTTP response helps you make your Virtual User have a dynamic behavior. Extracted variables can be injected in Logic Actions or HTTP Request Actions.

The first line displays the extracted variable name. This field is mandatory if you want to inject what you extract. The second line contains tab headers to access:
- Configuration, for more specific needs,
- Check, to validate the result of your XPath1 against an HTTP response.
Note
The response selector, on the right, lets you choose which HTTP response is used for configuring and checking the XPath1 Action. So if neither recorded responses nor Validate VU responses are available, you have to configure the XPath1 Action blindly.
Configuration¶
Query¶
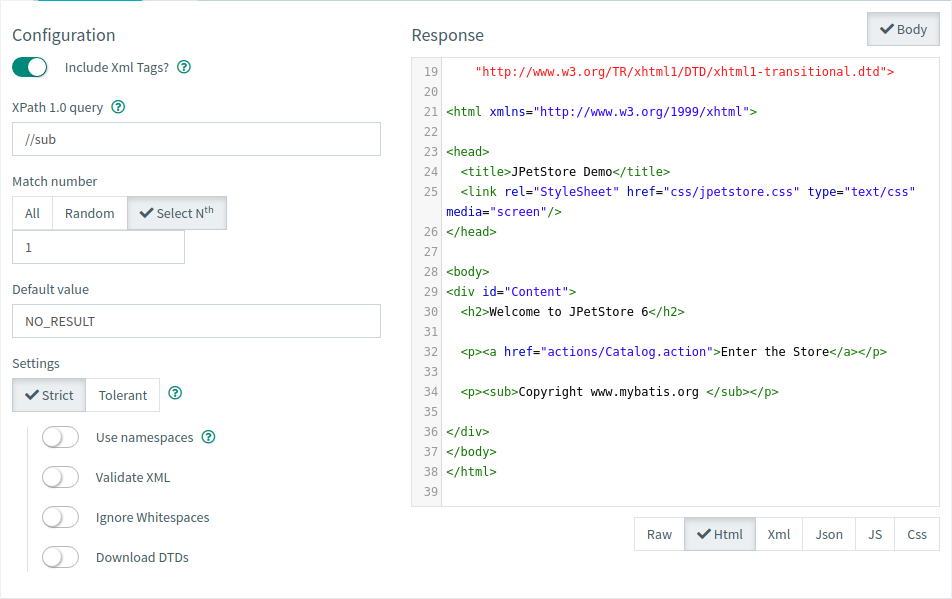
To configure a XPath1 extractor, the procedure is as follows:
- Fill the XPath 1.0 query field with a proper XPath expression,
- Select the Match number if your expression yields more than one result,
- Use Strict if you're working on a proper XML or Tolerant otherwise.
Tip
You can use third party tools like XPather to accelerate the design of your XPath expression. Just copy and paste the content of the response displayed on this page.
Parser settings¶
It is possible to use two different parsers for your XPath expressions, the first one uses the Xalan XPath parser, it should be used on proper XML content only.

| Name | Description |
|---|---|
| Use namespace | If activated, you should provide the namespace file and add the following user property : xpath.namespace.config=namespaces.properties |
| Validate XML | If active the document will be validated against its schema. |
| Ignore whitespaces | Used to ignore Element Whitespace. |
| Download DTDs | If selected, external DTDs are fetched. |
The second one uses Tidy to convert HTML to XML beforehand. This option should be used when working on HTML content, or any non-XML format that requires proper conversion beforehand.

| Name | Description |
|---|---|
| Quiet | When enabled, this option limits the output to report only document warnings and errors. |
| Report errors | If a Tidy error occurs, then set the Assertion accordingly. |
| Show warnings | This option specifies if Tidy should display warnings. |
Warning
Tidy will convert all elements and attribute names to lowercase. Tidy also attempts to correct improperly nested elements. Check its documentation for more info.
Check¶

To **check the result of a XPath1 ** action just click on the Check tab.
The check process is automatically launched when this tab is opened. It can also be manually started using the Refresh button.
A table contains the extracted values :
| Column name | Description |
|---|---|
| Extracted variable name | The name of the extracted variable. A single XPath1 Action can lead to multiple extracted variables. More information below. |
| Extracted variable value | The value of the extracted variable. |
Note
Multiple variables can be generated by a single XPath1 Action.
E.g. using the following HTML body :
<form method="post" action="/actions/Catalog.action">
<input name="keyword" type="text" />
<input name="searchProducts" type="submit" value="Search" />
<input type="hidden" name="_sourcePage" value="8UhFy3GTVvJLzGIdfPyNqtoclan" />
</form>
<form method="post" action="/actions/Account.action">
Please enter your username and password.
Username:<input name="username" type="text" />
Password:<input name="password" type="password" />
<input name="signon" type="submit" value="Login" />
<input type="hidden" name="_sourcePage" value="o_adZEJ7UO8IhGgRmltu2Ra6rSr" />
</form>
sourcePage with the XPath1 path value //input[@name='_sourcePage']/@value and a Select Nth match number:
sourcePage: the base variable, it contains the extracted value (or the default value), e.g.8UhFy3GTVvJLzGIdfPyNqtoclan
With an All match number, multiple variables are generated :
sourcePage: the default value as specified on the advanced tab,sourcePage_N: the Nth value extracted,sourcePage_matchNr: the number of values extracted, e.g. 2.
Warning
An extracted variable without name cannot be used for value injection.